Blog
Table of Content
Implement Claude Cowork Securely
Enterprise security guide for Claude Cowork: threat model, tiered admin configurations, prompt injection risks, and a setting-by-setting breakdown for both Cowork and Chat.
Specific use case in mind?
Get a customized report for your use case
Below, we walk through the threat model in depth, break out our recommended tiers of functionality and corresponding configurations you can set to mitigate risks for each tier, and then walk through every configuration you can set for Claude Cowork and what that might mean for your business.
Published: January 15, 2026; Last Updated: April 19, 2026
The Threat Model
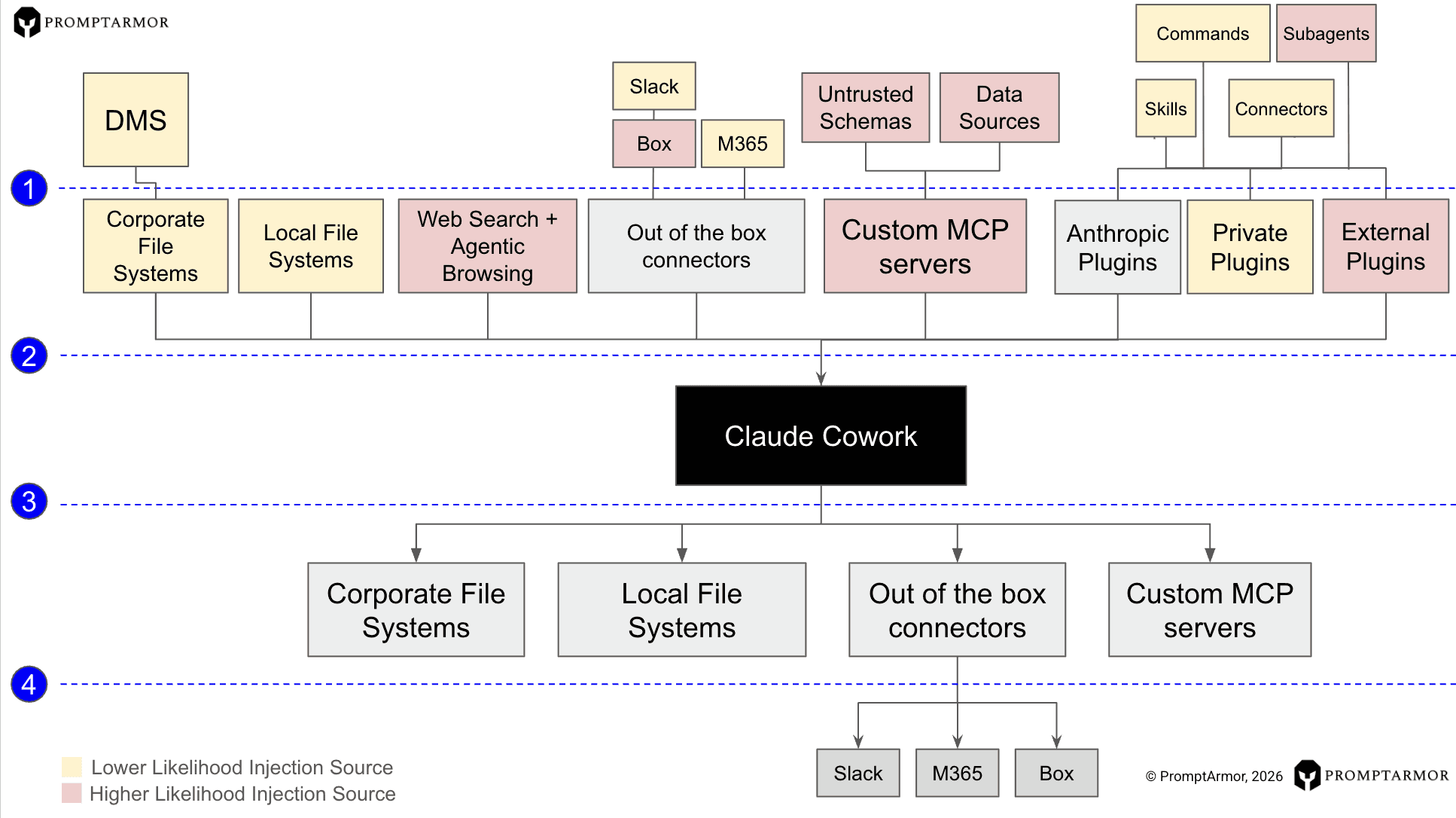
For Claude Cowork, the range of threats is greater because of the amount of untrusted input and the amount of confidential data it has access to. It also has a range of actions it can take on your system, which increases the downstream risk of your system being manipulated.
For example, an untrusted plugin downloaded from the internet could manipulate Claude into following an attacker’s instructions. You can see an example from Claude Code here that demonstrates how that could lead to data exfiltration: Hijacking Claude Code via Injected Marketplace Plugins
Because Claude has access to local file systems, it can also exfiltrate files that you have. Here is an example of Claude Cowork being manipulated by external data into exfiltrating confidential data: Claude Cowork exfiltrates files
This could also lead to phishing. For example, an untrusted piece of content could convince a user into submitting their credentials - a form of social engineering attack that allows an attacker to manipulate the LLM into crafting contextually relevant queries to convince a user to share their credentials. Example here with Slack: Data Exfiltration from Slack via Indirect Prompt Injection
Ultimately, the best way to “secure” Claude Cowork against novel indirect prompt injection vulnerabilities stems across four layers:
[1] implementing binary restrictions on access to types of external data sources that Claude can access (e.g., disallowing Slack access),
[2] configuring restrictions on that data (e.g., permitting only organizational admins to add skills),
[3] configuring restrictions on the types of actions that Claude can take based on output (e.g., restrict the sites Claude in Chrome can click on), and
[4] restrictions on the externally connected output surfaces (e.g., preventing automated link previews in Slack)
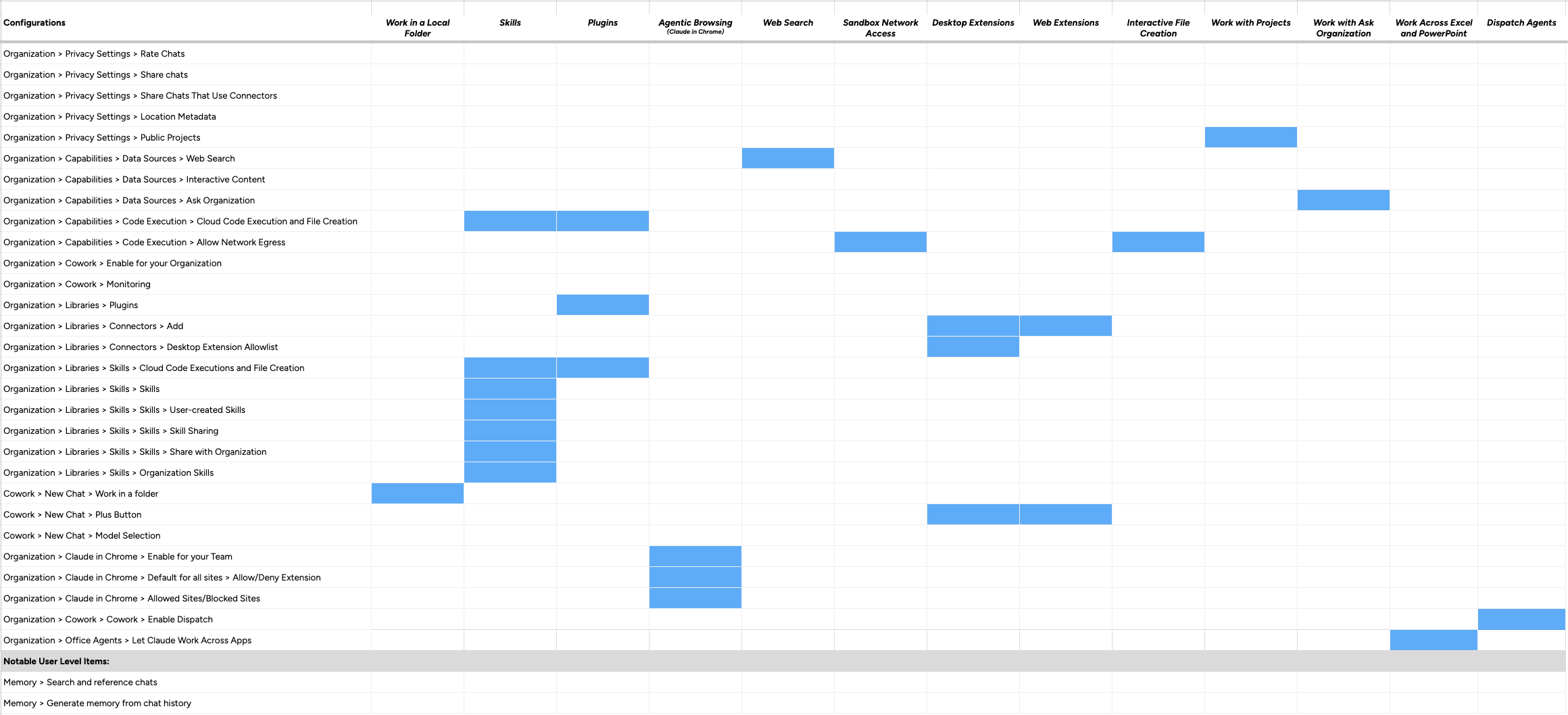
However, Claude’s settings are a bit interesting – not every single one operates in isolation. For example, to enable Skills, an organization must enable Cloud Code Execution and File Creation. Below, we walk through different combinations of ways you can set up Claude Cowork - that have different tradeoffs between functionality and risk - accounting for what combinations are actually feasible given what settings can be on (or off) at the same time.
Configurations vs Functionality
Below are our recommended Tiers of Claude Cowork usage depending on your organization’s risk tolerance. Maximizing functionality requires risk tradeoffs depending on the threat model.
Assessing skills, plugins, or connectors?
See the risk
All “functionality” for Claude
Functionality | Tier 1 | Tier 2 | Tier 3 |
Work in a Local Folder | Y | Y | Y |
Skills | Y | Restricted | N |
Plugins | Y | Restricted | N |
Agentic Browsing | Y | Restricted | Restricted |
Web Search | Y | Y | Y |
Sandbox Network Access | Y | Restricted | N |
Desktop Extensions | Restricted | Restricted | N |
Web Extensions | Restricted | Restricted | N |
Interactive File Creation | Y | Y | Y |
Work with Projects | Y | N | N |
Work with Ask Organization | Y | Y | N |
Work across Excel and PPT | Y | N | N |
Dispatch Agents | Y | N | N |
Tier 1: Maximized functionality
In Tier 1, you get access to all of Claude Cowork’s functionality. However, this greatly increases the risk surface. Injections can come from Skills and Plugins that users upload, from local folders that contain untrusted data, web search, desktop and web extensions. Additionally, Claude can work across apps via Claude for PowerPoint and Claude for Excel which can be orchestrated from Cowork.
Note: Desktop extensions and web extensions are still ‘restricted’ in this tier, as they must be individually added by an organization.
NIST AI RMF Coverage with Tier 1 Configuration
Not sure what these categories are? See our NIST AI RMF Reference
GOVERN | MAP | MEASURE | MANAGE |
|---|---|---|---|
1, 2 | 1, 2 | 1 |
There are some useful settings that you should turn on regardless, even if you want to maximize functionality:
For Claude Cowork
Configuration | Explanation |
|---|---|
| Allow people to rate Claude's responses and share that feedback with Anthropic.
|
| Cowork supports OpenTelemetry (OTel) events for monitoring and observability. You can enable this for granular observability without impacting any functionality. |
For Claude Chat (these settings do not apply to Claude Cowork)
Configuration | Explanation |
| Allow Claude to use coarse location metadata (city/region) to improve product experiences for your team members. Ultimately, these settings do not reduce your risk exposure to indirect prompt injection for Cowork. However, these configurations allow you to maximize functionality while avoiding some risks and enabling telemetry to gain observability. |
Tier 2: Balancing functionality with risks
In tier two, functionality tradeoffs are balanced against risks, restricting control over connected resources to the organization-level where possible and limiting access to sensitive org-specific data (e.g., connection to Excel and PowerPoint). Claude can perform meaningful automation and file work using org-controlled tools and integrations. Prompt injection risk is managed by restricting untrusted data sources (user skills, plugins, unvetted domains) while keeping the org's approved toolset functional.
What's enabled:
Organization-vetted skills — org-approved skills can be used; users cannot upload their own
Skill sharing — allowed within one's organization
Organization-configured plugins — org-designated plugins auto-installed; users cannot add their own
Network egress (package managers only) — Claude can install packages for data analysis; additional approved domains can be allowlisted
Claude in Chrome — browser automation enabled for most sites, with an org-managed blocklist for sensitive sites
Desktop extensions — org-uploaded extensions available; allowlist controls what users can install
Web connectors — org-configured connectors available to team members
Always allow mode for connectors — prohibited, encouraging human in the loop approval
Skip all approvals mode — prohibited, encouraging human in the loop approval
Public Projects — access to public projects prohibited, limiting injection risks
Ask Organization — allows access trusted org-specific data
M365 Integrations — orchestrating Claude for PowerPoint and Excel prohibited limiting varied trust level data processing
Dispatch agents — disabled, preventing autonomous agents from interacting with one's computer without substantial oversight
NIST AI RMF Coverage with Tier 2 Configuration
GOVERN | MAP | MEASURE | MANAGE |
|---|---|---|---|
1, 2, 3, 4, 6 | 1, 2, 3, 4 | 2 | 1, 2, 3, 4 |
Configuration | Explanation |
|---|---|
Note: This path reflects the setting when viewed from the desktop app. In the web browser, it is displayed as 'Code Execution and File Creation' (no 'Cloud'). | Allow Claude to execute code on a server and create and edit docs, spreadsheets, presentations, PDFs, and data reports. Required for skills to be enabled. Available on web and desktop.
|
| Turn skills on or off for everyone in your organization, including admin-managed organization skills. Requires 'Code execution and file creation' to be enabled to use. Skills might contain executable code. Team members should be careful when using skills from unknown sources. |
| Allow team members to upload or create their own skills. Turn off to lock your org to approved skills only. |
| Allow team members to share skills with each other. |
| Allow team members to share skills with the entire organization. |
| Manage skills that can be viewed and used by anyone in your organization.
|
| Allows organizations to designate plugins that will be blocked, automatically installed, or made optionally available to organization members.
|
| Members can let Claude share context between apps like Excel and PowerPoint. |
| Allow members to create persistent Cowork agents that can control their computer to autonomously work on tasks. Persistent agents receive instructions from any logged in device on the same account and can access files, apps and websites on their computer.
|
| Give Claude network access to install packages and libraries in order to perform advanced data analysis, custom visualizations, and specialized file processing. Monitor chats closely as this comes with security risks. |
|
|
| Allow team members to use the Claude in Chrome extension. Configure site permissions after enabling.
|
|
|
| Claude in Chrome cannot be used on these websites.
Note: during testing, the blocklist did not appear to restrict access. |
| Limit the extensions that your team can install on their desktop. When enabled, users can only install desktop extensions that have been added to the list above. Via this allowlist, organizations should configure which desktop extensions they would like to allow. Note, ‘desktop extensions (DXT)’ are being renamed to MCP Bundles (MCPB). |
| Control which connectors your team members have access to. Use this menu to add connectors for use within one’s organization. |
| When enabled, users can let Claude act without asking for approval—including using tools, editing files, and browsing websites. This can put organizational data at risk.
|
| Let members choose "Always allow" when approving connector tools in Cowork. This increases risk from prompt injection — content from connected apps could cause Claude to take unintended actions without per-use approval. Learn more
|
| All users in an organization can see and start chats in public projects.
|
| Allow your team members to search across your organization's connected data sources and knowledge bases for more comprehensive results.
|
Here are relevant configurations for Claude Chat (does not apply to Cowork):
Configuration | Explanation |
|---|---|
|
|
|
|
|
|
Tier 3: Locked Down
Tier 3 prioritizes security above all else, disabling most dynamic or external-facing capabilities. Claude operates as a mostly self-contained assistant with no access to external data, executable code, or connected services. Prompt injection surface is minimal.
What's disabled:
Code execution and file creation (cloud) — no server-side code execution and file creation
Network egress — no package installs or external domain access from the sandbox
Skills — All skills blocked, including user-uploaded skills, and skill sharing is prohibited
Plugins — user-uploaded plugins blocked
Web connectors and desktop extensions — no external service integrations
Always allow mode for connectors — prohibited, encouraging human in the loop approval
Skip all approvals mode — prohibited, encouraging human in the loop approval
Claude in Chrome — no browser automation
Ask Organization — users cannot access or start chats based on data from ‘Ask Organization’
Public Projects — users cannot access or start chats in shared projects
M365 Integration — users cannot orchestrate Claude in Excel or PowerPoint from Cowork
Dispatch agents — disabled, preventing autonomous agents from interacting with one's computer without substantial oversight
What's enabled:
OTel monitoring — full observability with no functionality impact
Local Cowork operations remain available (file access and chat attachments are user-level controls, not disabled by default)
NIST AI RMF Coverage with Tier 3 Configuration
GOVERN | MAP | MEASURE | MANAGE |
|---|---|---|---|
1, 2, 3, 4, 5, 6 | 1, 2, 3, 4, 5 | 1, 2, 3 | 1, 2, 3, 4 |
Here are relevant configurations for Cowork:
Configuration | Explanation |
|---|---|
|
|
| All users in an organization can see and start chats in public projects.
|
|
|
| Members can let Claude share context between apps like Excel and PowerPoint. |
|
|
Alternatively, if specific domains must be accessible from the Cowork sandbox, configure:
|
|
|
|
|
|
|
|
| When enabled, users can let Claude act without asking for approval—including using tools, editing files, and browsing websites. This can put organizational data at risk.
|
| Limit the extensions that your team can install on their desktop. When enabled, users can only install desktop extensions that have been added to the list above.
|
| Control which connectors your team members have access to.
|
| Let members choose "Always allow" when approving connector tools in Cowork. This increases risk from prompt injection — content from connected apps could cause Claude to take unintended actions without per-use approval. Learn more
|
| Allow members to create persistent Cowork agents that can control their computer to autonomously work on tasks. Persistent agents receive instructions from any logged in device on the same account and can access files, apps and websites on their computer.
|
| Members can let Claude share context between apps like Excel and PowerPoint. |
Note: This path reflects the setting when viewed from the desktop app. In the web browser, it is displayed as 'Code Execution and File Creation' (no 'Cloud'). |
|
| Turn skills on or off for everyone in your organization, including admin-managed organization skills. Requires 'Code execution and file creation' to be enabled to use. Skills might contain executable code. Team members should be careful when using skills from unknown sources. |
| Allow team members to upload or create their own skills. Turn off to lock your org to approved skills only. |
| Allow team members to share skills with each other. |
| Allow team members to share skills with the entire organization. |
| Manage skills that can be viewed and used by anyone in your organization.
|
| Disallow users in Cowork from accessing and operating on the contents of a local directory. |
| Disallow users in Cowork to add files and photos, include a Project, or select Connectors for the chat. |
| Disallow team members from use the Claude in Chrome extension. |
|
|
Here are relevant configurations for Claude Chat (does not apply to Cowork):
Configuration | Explanation |
|---|---|
|
|
|
|
|
|
|
|
| Let Claude display maps, images, and other visual content using third-party services. This does not apply to Cowork |
| This turns off the ability for team members to work with artifacts that use data from external sources – as those external sources increase risk exposure to indirect prompt injections. |
| Allow Claude to search for relevant details in past chats. Learn more. |
| Allow Claude to remember relevant context from your chats. This setting controls memory for both chats and projects. Learn more. |
Additional Controls and NIST Mappings
Beyond the Cowork-specific configurations above, the following infrastructure controls determine whether your tier configuration is actually enforceable. Without identity, access, monitoring, and data governance controls in place, even a Tier 3 lockdown can be circumvented; for example, by users switching to personal accounts.
These action items should be implemented regardless of which tier is selected, then combined with the tier-specific Cowork configurations.
NIST AI RMF Coverage Gained from Additional Controls Applied
GOVERN | MAP | MEASURE | MANAGE |
|---|---|---|---|
1, 2, 3, 6 | 3 | 2, 3 | 1, 4 |
Action Item | Description & NIST Mapping |
|---|---|
Configure SSO and require it for Console and Claude | Enforces the organizational authentication boundary. Without SSO, users can authenticate outside org controls, undermining every tier configuration. Maps to GOVERN 1 (controls based on org risk priorities) and MEASURE 2 (security and resilience evaluated). |
Configure SCIM directory sync and enable group mappings | Automates account lifecycle and role assignment from your IdP. Ensures deprovisioned employees lose Cowork access immediately. Maps to GOVERN 2 (roles and responsibilities documented and clear) and GOVERN 3 (human-AI oversight roles defined). |
Configure IP allowlisting | Prevents access from untrusted networks or unmanaged devices. Maps to MEASURE 2 (security and resilience evaluated). |
Restrict organization access and creation | Prevents shadow AI organizations under your domain, blocks personal account creation with org emails, and removes open invite paths that could allow unvetted users into the org. Maps to GOVERN 1 (controls based on org priorities and mechanisms to inventory AI systems). |
Enable shortened session length | Limits session duration before reauthentication, reducing exposure window if a session is compromised. Maps to MEASURE 2 (security and resilience). |
Configure RBAC with role-based feature access | Differentiate Code Execution, Memory, Web Search, Claude Code, and Cowork permissions by user group. Maps to GOVERN 3 (policies to differentiate roles for human-AI configurations) and MAP 3 (human oversight processes defined per org policy). |
Enable the Compliance API | Streams compliance data from Claude Chat for visibility. Cowork activity is currently excluded, but this is critical for holistic monitoring of your Claude deployment. Maps to MEASURE 2 (system monitored in production) and MEASURE 3 (approaches to track emergent risks). |
Configure data retention and deletion policies | Define how long chats and uploads are retained. Enable separate retention periods for chats vs. projects to apply stricter retention to project data that may contain more sensitive or persistent context. Maps to MANAGE 4 (post-deployment monitoring including change management) and GOVERN 6 (policies addressing third-party AI data risks). |
Disable chat sharing | Disabling chat sharing prevents exposure of AI interaction data between users of different privilege levels. Disabling sharing of chats that use connectors is especially important as those chats may surface data from connected systems that the recipient should not have access to. Maps to MEASURE 2 (privacy risk examined and documented). |
Develop a phased rollout plan | Start with Cowork disabled, enable for a pilot group with restrictive settings, establish monitoring baselines, then expand based on observed risk. Maps to GOVERN 1 (processes to determine needed risk management activities based on risk tolerance) and MANAGE 1 (determination on whether deployment should proceed). |
Conduct AI risk management training for Cowork users | Include prompt injection recognition, suspicious action identification, and safe file handling. Maps to GOVERN 2 (personnel receive AI risk management training consistent with policies and procedures). |
Establish an AI/Cowork-specific incident response plan | Define escalation paths, containment procedures (e.g., disabling Cowork org-wide), and communication protocols for prompt injection incidents or data exfiltration. Maps to MANAGE 2 (procedures for unknown risk response) and MANAGE 4 (incidents communicated, tracked, recovered). |
Document accepted residual risks and define exit criteria | For each tier, document what risks remain unmitigated (e.g., audit log gap, prompt injection surface) and the conditions under which Cowork would be disabled. Maps to MANAGE 1 (residual risks documented) and GOVERN 1 (decommissioning processes in place). |
Helpful Resources |
|---|
All configurations, granularly
Organization > Privacy Settings > Rate Chats
Allow people to rate Claude's responses and share that feedback with Anthropic.
Applies to Cowork? Yes.
Organization > Privacy Settings > Share chats
Allow people to share chats with others in your org.
Applies to Cowork? No, there is no option to share Cowork chats.
Organization > Privacy Settings > Share Chats That Use Connectors
Allow people to share chats that use connectors with others in your org. Recipients will see Claude's response, but not the data from the connector.
Applies to Cowork? No, there is no option to share Cowork chats.
Organization > Privacy Settings > Location Metadata
Allow Claude to use coarse location metadata (city/region) to improve product experiences for your team members.
Applies to Cowork? No, testing indicates metadata is not passed to Cowork as context.
Organization > Privacy Settings > Public Projects
All users in an organization can see and start chats in public projects.
Applies to Cowork? Yes. Users can start a Cowork session based on projects.
Organization > Capabilities > Data Sources > Web Search
Turn on web search for your team members.
Applies to Cowork? No. Web search is always enabled for Cowork.
Organization > Capabilities > Data Sources > Interactive Content
Let Claude display maps, images, and other visual content using third-party services. Learn how your data is used
Applies to Cowork? No. Cowork does not display interactive inline content. Cowork creates files and supports an interactive viewer, which is a separate functionality.
Organization > Capabilities > Data Sources > Ask Organization
Allow your team members to search across your organization's connected data sources and knowledge bases for more comprehensive results.
Applies to Cowork? Yes. Users can start a Cowork session based on Ask Organization that carries organizational context to the Cowork session.
Organization > Capabilities > Visuals > Enable Artifact Connectors
Let team members work with artifacts that use data from external sources. Learn more
Applies to Cowork? No. Cowork creates files and supports an interactive viewer, but these are not Artifacts.
EDIT 4/12/2026: This setting has been removed from Claude. Artifacts are no longer governable at the admin level.
Organization > Capabilities > Visuals > Inline visualizations
Allow Claude to generate interactive visualizations, charts, and diagrams directly in the conversation for members of your organization.
Applies to Cowork? No. Cowork creates files and supports an interactive viewer, but these are not 'Inline Visualizations'.
Organization > Office Agents > Let Claude Work Across Apps
Members can let Claude share context between apps like Excel and PowerPoint.
Applies to Cowork? Yes. Users can orchestrate Claude in Excel or PowerPoint via Cowork.
Organization > Capabilities > Code Execution > Cloud Code Execution and File Creation
Allow Claude to execute code on a server and create and edit docs, spreadsheets, presentations, PDFs, and data reports. Required for skills to be enabled. Available on web and desktop.
Applies to Cowork? Somewhat. Cowork can natively perform most of these capabilities locally, but this is relevant because the setting must be toggled 'on' to enable skill uploads, which are applicable to Cowork.
Note: This path reflects the setting when viewed from the desktop app. In the web browser, it is displayed as 'Code Execution and File Creation' (no 'Cloud').
Organization > Capabilities > Code Execution > Allow Network Egress
Give Claude network access to install packages and libraries in order to perform advanced data analysis, custom visualizations, and specialized file processing. Monitor chats closely as this comes with security risks.
Applies to Cowork? Yes.
Organization > Cowork > Enable for your Organization
Your network egress settings will apply. Cowork is a research preview—some enterprise features like audit logs, compliance API, and data exports are not currently available. Learn more about using Cowork safely
Applies to Cowork? Yes.
Organization > Cowork > Permissions > Allow "Skip all approvals" mode
When enabled, users can let Claude act without asking for approval—including using tools, editing files, and browsing websites. This can put organizational data at risk.
Applies to Cowork? Yes.
Organization > Cowork > Permissions > Allow “Always allow” for connector tools
Let members choose "Always allow" when approving connector tools in Cowork. This increases risk from prompt injection — content from connected apps could cause Claude to take unintended actions without per-use approval. Learn more
Applies to Cowork? Yes.
Organization > Cowork > Cowork > Enable Dispatch
Allow members to create persistent Cowork agents that can control their computer to autonomously work on tasks. Persistent agents receive instructions from any logged in device on the same account and can access files, apps and websites on their computer.
Applies to Cowork? Yes.
Organization > Cowork > Monitoring
Cowork supports OpenTelemetry (OTel) events for monitoring and observability. Cowork reuses Claude Code's OTel events schema via the Claude Agent SDK. Learn more
Applies to Cowork? Yes.
Organization > Libraries > Plugins
Allows organizations to designate plugins that will be blocked, automatically installed, or made optionally available to organization members.
Applies to Cowork? Yes.
Note: during testing, when organization-level plugins were installed by default for users, it was observed that the org-level plugins were installed but did not appear operable without Skills enabled.
Organization > Libraries > Connectors
Control which web and desktop connectors your team members have access to.
Applies to Cowork? Yes.
Organization > Libraries > Connectors > Desktop Extension Allowlist
Limit the desktop extensions that your team can install on their desktop.
When enabled, users can only install desktop extensions that have been added to the list above.
Applies to Cowork? Yes.
Organization > Libraries > Skills > Cloud Code Execution and File Creation
Allow Claude to execute code on a server and create and edit docs, spreadsheets, presentations, PDFs, and data reports. Required for skills to be enabled. Available on web and desktop.
Applies to Cowork? Somewhat. Cowork can natively perform most of these capabilities locally, but this is relevant because the setting must be toggled 'on' to enable skill uploads, which are applicable to Cowork.
Note: This path reflects the setting when viewed from the desktop app. In the web browser, it is displayed as 'Code Execution and File Creation' (no 'Cloud').
Organization > Libraries > Skills > Skills
Turn skills on or off for everyone in your organization, including admin-managed organization skills. Requires 'Code execution and file creation' to be enabled to use. Skills might contain executable code. Team members should be careful when using skills from unknown sources.
Applies to Cowork? Yes. In order for skills to be uploaded, this setting must be enabled. In order for plugins to be used, this setting must be enabled.
Note: during testing, it was observed that disabling this setting served to prevent users from adding their own plugins.
Organization > Libraries > Skills > User-created skills
Allow team members to upload or create their own skills. Turn off to lock your org to approved skills only.
Applies to Cowork? Yes.
Organization > Libraries > Skills > Skill sharing
Allow team members to share skills with each other.
Applies to Cowork? Yes.
Organization > Libraries > Skills > User-created skills
Allow team members to share skills with the entire organization.
Applies to Cowork? Yes.
Organization > Libraries > Skills > Organization Skills
Manage skills that can be viewed and used by anyone in your organization.
Applies to Cowork? Yes.
Cowork > New Chat > Work in a folder
Allows Cowork to access and operate on the contents of a local directory.
Cowork > New Chat > Plus Button
Allows users to add files and photos, include a Project, or select Connectors for the chat.
Cowork > New Chat > Model Selection
Allows users to select what model will be used for Cowork's response.
Organization > Claude in Chrome > Enable for your Team
Allow team members to use the Claude in Chrome extension. Configure site permissions after enabling.
Applies to Cowork? Yes.
Organization > Claude in Chrome > Default for all sites > Allow/Deny Extension
Set default access for your team
Applies to Cowork? Yes.
Note: During testing, inconsistent behavior was observed from this setting.
Organization > Claude in Chrome > Allowed Sites/Blocked Sites
Claude in Chrome can/cannot (depending on whether the default is allow or deny) be used on these websites.
Applies to Cowork? Yes.
Note: During testing, inconsistent behavior was observed from this setting.
Notable User Level Items:
Memory > Search and reference chats
Allow Claude to search for relevant details in past chats. Learn more.
Applies to Cowork? No. Cowork cannot reference memories across conversations.
Memory > Generate memory from chat history
Allow Claude to remember relevant context from your chats. This setting controls memory for both chats and projects. Learn more.
Applies to Cowork? Yes. Cowork can create memories, only within Projects.
Vendor Risk & Third-Party Assessment
Claude Cowork Security FAQ
Security & Risk
Claude Cowork introduces a fundamentally different threat surface than a standard chatbot. It is a local AI agent that can execute code in a VM, read and write files on the user's machine, browse the web with the user's cookies, and run scheduled tasks unattended.
The primary risks are:
Prompt injection — Anthropic identifies this as the primary risk. Malicious instructions hidden in documents, emails, or web pages can hijack Claude's actions. Anthropic self-reports an approximately 1% attack success rate on Claude in Chrome specifically, even after mitigations. In January 2026, research demonstrated that indirect prompt injection could cause Cowork to upload user files to an attacker-controlled Anthropic account.
Audit gap — Cowork activity is not captured in Anthropic's Audit Logs, Compliance API, or Data Exports.
Monitoring limitations — Anthropic's own safety guidance acknowledges that 'you shouldn't expect to validate every individual command' — instead advising users to watch for unexpected patterns.
Personal account use — On non-Enterprise plans, tenant restrictions are not available, meaning users can switch to a personal Pro/Max account on the same machine outside of organizational controls.
Compliance
No. Anthropic explicitly states: do not enable Cowork for regulated workloads. Cowork activity is excluded from all three governance mechanisms: Audit Logs, Compliance API, and Data Exports.
Until Anthropic closes the audit log gap, Cowork cannot satisfy the logging and monitoring requirements of SOC 2, HIPAA, GDPR, or similar frameworks.
Data Management
Cowork stores conversation history locally on users' computers. Per Anthropic, this data is not subject to Anthropic's standard data retention policies and cannot be centrally managed or exported by admins.
This is a different model than cloud-hosted Claude conversations — admins should understand that Cowork data governance follows local device management, not Anthropic's cloud retention controls.
Anthropic does provide OpenTelemetry integration that tracks usage, costs, and tool activity for Cowork. Organizations should review Anthropic's current data usage policy and Commercial Terms of Service to confirm training opt-out status for their specific plan tier.
Access Control
You control which local files Claude can access. However, there are important caveats beyond folder access.
Cowork can browse the web using your cookies and session state via Claude in Chrome — and when JavaScript execution is enabled for a site, Claude can access the same data your browser can on that page, including login sessions and stored website data.
Cowork can also interact with connected MCP and plugin integrations, which Anthropic warns 'expand what Claude can do, but each one introduces new ways for attacks to reach Claude.'
The effective data exposure is the union of shared folders, browser session access, and any connected integrations — not just the folders you designate.
Enterprise Configuration
The most notable differential: on Team plans, Chrome is on by default, and there is no mechanism to prevent users from switching to a personal account. Enterprise plans are required for tenant restrictions.
Disable Cowork entirely — Available on both Team and Enterprise.
Chrome extension — Enabled by default on Team, disabled by default on Enterprise.
Tenant restrictions — Not available on Team. Available on Enterprise only.
Chrome site allowlists/blocklists — Available on both.
Plugin marketplace management — Available on both.
OpenTelemetry monitoring — Available on both.
Audit logs for Cowork activity — Not available on either plan.
Cowork toggle — Organization owners navigate to Organization settings > Capabilities to toggle Cowork off entirely. Per Anthropic, Cowork will be on by default when the research preview launches. Granular per-user or per-role controls are not available during the research preview.
Chrome extension — Managed separately from Cowork itself. On Enterprise plans, it is disabled by default. On Team plans, it is enabled by default. Admins can configure site allowlists and blocklists via Organization settings > Claude in Chrome.
Tenant restrictions — Enterprise-only. Configure your network proxy to inject the anthropic-allowed-org-ids header for Claude traffic. Supported on Zscaler, Palo Alto Prisma, Cato Networks, Netskope, and generic HTTPS proxies. TLS inspection is required.
Plugin management — Owners can create curated plugin marketplaces with per-plugin controls: auto-install, available, or not available.
Monitoring
This is the most significant operational gap. Anthropic explicitly states that Cowork activity is not captured in Audit Logs, Compliance API, or Data Exports, and that if your organization requires audit trails for compliance purposes, do not enable Cowork for regulated workloads.
The one monitoring mechanism Anthropic does provide is OpenTelemetry: Team and Enterprise owners can track usage, costs, and tool activity across their teams. However, Anthropic is clear that this doesn't replace audit logging for compliance purposes.
Beyond what Anthropic provides, organizations should evaluate whether their existing endpoint security stack — EDR, DLP, network monitoring — provides sufficient compensating visibility for Cowork's local activity before enabling it beyond a pilot.
Prompt Injection
Prompt injection risk with Cowork is categorically higher than with the standard Claude chatbot because there are more ways Cowork can act. It reads, writes, and deletes files, browses the web, executes code, and interacts with external systems. A successful prompt injection in Cowork can exfiltrate files, delete data, send messages on your behalf, or execute code.
The attack surface includes any untrusted content that enters Claude's context: web pages visited through Chrome, documents opened for processing, emails, and files from shared drives.
Anthropic deploys content classifiers that scan untrusted input and flag potential injections, but their own reporting acknowledges a non-zero success rate — approximately 1% attack success against their internal Best-of-N attacker for Claude in Chrome.
Yes. In January 2026, two days after Cowork's launch, PromptArmor demonstrated that Claude Cowork could be manipulated through indirect prompt injection to exfiltrate user files.
The attack chain worked as follows:
1. The attacker hides malicious instructions in a document or web page that Claude processes.
2. The injection instructs Claude to use curl to upload specified files to the Anthropic file upload API.
3. The injection provides the attacker's API key, so files are uploaded to the attacker's account.
4. Cowork's VM restricted outbound network access to most domains, but the Anthropic API was accessible from within the VM — so the upload succeeded.
For the full technical write-up, see the PromptArmor research blog.
Integrations
Anthropic's own safety guidance warns that desktop extensions (MCPs) and plugins expand what Claude can do, but each one introduces new ways for attacks to reach Claude. Plugins bundle skills, connectors, and sub-agents into a single package, meaning a single install can significantly expand Cowork's scope of action.
Anthropic recommends sticking to verified extensions from the Claude Desktop directory, carefully evaluating the permissions any extension or plugin requests before installing, and using plugin marketplace controls to set per-plugin installation preferences.
For organizations, the key risk is that an employee installing an unvetted MCP server or plugin creates an uncontrolled integration point that bypasses your evaluated security posture.
Decision Making
This depends on your risk tolerance, plan tier, and use case.
Allow with controls if — You are on an Enterprise plan, can enforce tenant restrictions, have curated your plugin marketplace, have OpenTelemetry configured, and the use case involves non-sensitive, non-regulated data.
Allow in limited pilot if — You are on a Team plan, can accept the lack of tenant restrictions, and want to evaluate productivity gains in a limited environment (e.g., non-sensitive local folders only) with Claude in Chrome disabled.
Do not allow yet if — Your workloads involve regulated data (HIPAA, PCI, SOX), you require audit trails for compliance, you cannot deploy compensating monitoring controls, or you are on a plan tier that lacks admin controls.
We recommend against treating the Cowork decision as binary (allow/block). A phased rollout is more practical: start with Cowork disabled, enable it for a pilot group with restrictive settings, establish monitoring, then expand based on observed risk.
Research preview means Cowork is not yet a generally available, production-grade product. Concretely:
- Security controls and features are still being developed — granular controls by user or role are not available during the research preview.
- The audit log gap is acknowledged but not yet resolved.
- Prompt injection risk remains non-zero.
- Cowork's behavior and capabilities may change between preview updates.
For TPRM purposes, treat Cowork as you would any pre-GA vendor capability: document the accepted risk, establish compensating controls, define exit criteria for when you would disable it, and review the risk posture at each Anthropic product update.
On Enterprise plans, you can enforce tenant restrictions via HTTP header injection that prevents users from authenticating with non-organizational accounts. This is the only reliable control.
On Team plans, there is no mechanism to prevent this. A user can sign out of the organizational account, sign into a personal Pro or Max account, and use Cowork with zero organizational guardrails: no connector restrictions, no defensive instructions, no admin visibility. All file access is governed by the user's OS-level permissions.
This is why Enterprise-tier deployment is strongly recommended for organizations with sensitive data on employee machines.
Both products can execute code, both can integrate with the Claude in Chrome extension with its associated prompt injection risks, and both can run tasks without active user supervision.
The Claude Code CLI runs on a user's device with access to the local file system. Claude Code via the Desktop can use a cloud VM environment and also operate on local directories. Claude Cowork runs a local VM with optional access to a local directory, but for some features like skills, code execution can occur in the cloud.
Organizations deploying both products should evaluate each independently within the context of what features and configurations will be enabled or restricted, rather than seeking to discern if one is categorically safer than the other.
One important note: Anthropic explicitly states that Cowork activity is not captured in Audit Logs, Compliance API, or Data Exports. Claude Code does not carry the same exclusion in Anthropic's documentation. This means organizations should understand that their ability to audit and govern Cowork activity is currently more limited than for Claude Code.